Chinese Hackers Deploy Fake News Site To Infect Government, Energy Targets – TechNewsWorld
A Chinese cyber espionage group has been using a fake news site to infect government and energy industry targets in Australia, Malaysia and Europe with malware, according to a blog posted online Tuesday by Proofpoint and PwC Threat Intelligence.
The group is known by several names, including APT40, Leviathan, TA423 and Red Ladon. Four of its members were indicted by the U.S. Department of Justice in 2021 for hacking a number of companies, universities and governments in the United States and worldwide between 2011 and 2018.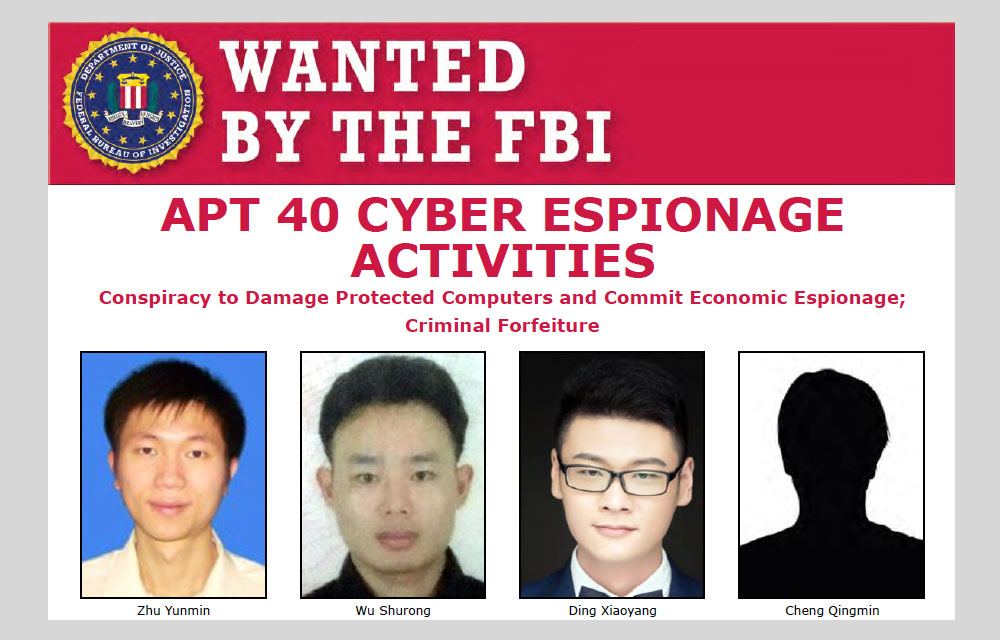
APT40 members indicted by United States Department of Justice in 2021 / Image Credit: FBI
The group is using its fake Australian news site to infect visitors with the ScanBox exploitation framework. “ScanBox is a reconnaissance and exploitation framework deployed by the attacker to harvest several types of information, such as the target’s public-facing IP address, the type of web browser used and its configuration,” explained Proofpoint Vice President for Threat Research and Detection Sherrod DeGrippo.
“This serves as a setup for the stages of information gathering that follow and potential follow-on exploitation or compromise, where malware could be deployed to gain persistence on the victim’s systems and allow the attacker to perform espionage activities,” she told TechNewsWorld.
“It creates an impression of the victim’s network that the actors then study and decide the best route to take to achieve further compromise,” she said.
“Watering Hole” attacks that use ScanBox appeal to hackers because the point of compromise isn’t within a victim’s organization, added John Bambenek, a principle threat hunter at Netenrich, a San Jose, Calif.-based IT and digital security operations company.
“So, there is difficulty detecting that information is being discretely stolen,” he told TechNewsWorld.
According to the Proofpoint/PwC blog, the TA423 campaign primarily targeted local and federal Australian government agencies, Australian news media companies, and global heavy industry manufacturers which conduct maintenance of fleets of wind turbines in the South China Sea.
It noted that phishing emails for the campaign were sent from Gmail and Outlook email addresses, which Proofpoint believes with “moderate confidence” were created by the attackers.
Subject lines in the phishing emails included “Sick Leave,” “User Research,” and “Request Cooperation.”
The threat actors would frequently pose as an employee of the fictional media publication “Australian Morning News,” the blog explained, and provide a URL to their malicious domain, soliciting targets to view their website or share research content that the website would publish.
If a target clicked the URL, they’d be sent to the fake news site and be served up, without their knowledge, the ScanBox malware. To give their bogus website credibility, the adversaries posted content from legitimate news sites, such as the BBC and Sky News.
ScanBox can deliver its code in two ways: in a single block, which gives an attacker access to the malware’s full functionality immediately, or as a plug-in, modular architecture. The TA423 crew chose the plug-in method.
According to PwC, the modular route can help avoid crashes and errors that would alert a target that their system is under attack. It’s also a way to reduce the visibility of the attack to researchers.
As these kinds of campaigns show, phishing remains the tip of the spear used to penetrate many organizations and steal their data. “Phishing sites have seen an unexpected surge in 2022,” observed Monnia Deng, director of product marketing at Bolster, a provider of automated digital risk protection, in Los Altos, Calif.
“Research has shown that this problem has skyrocketed tenfold in 2022 because this method is easy to deploy, effective and a perfect storm in a post-pandemic digital era of work,” she told TechNewsWorld.
DeGrippo maintained that phishing campaigns continue to work because threat actors are adaptive. “They use current affairs and overall social engineering techniques, many times preying off a target’s fears and sense of urgency or importance,” she said.
A recent trend among threat actors, she continued, is attempting to increase the effectiveness of their campaigns by building trust with intended victims through extended conversations with individuals or through existing conversation threads between colleagues.
Roger Grimes, a defense evangelist with KnowBe4, a security awareness training provider, in Clearwater, Fla. asserted that social-engineering attacks are particularly resistant to technical defenses.
“Try as hard as we might, so far, there have been no great technical defenses that prevent all social engineering attacks,” he told TechNewsWorld. “It’s particularly hard because social engineering attacks can come over email, phone, text message, and social media.
Even though social engineering is involved in 70% to 90% of all successful malicious cyberattacks, it’s the rare organization that spends more than 5% of its resources to mitigate it, he continued.
“It’s the number one problem, and we treat it like a small part of the problem,” he said. “It’s that fundamental disconnect that allows attackers and malware to be so successful. As long as we don’t treat it as the number one problem, it will continue to be the primary way that attackers attack us. It’s just math.”
While TA423 used email in its phishing campaign, Grimes noted that adversaries are moving away from that approach.
“Attackers are using other avenues, such as social media, SMS text messages, and voice calls more often to do their social engineering,” he explained. “That’s because many organizations focus almost exclusively on email-based social engineering and the training and tools to fight social engineering on the other types of media channels are not at the same level of sophistication in most organizations.”
“That is why it is crucial that every organization create a personal and organizational culture of healthy skepticism,” he continued, “where everyone is taught how to recognize the signs of a social engineering attack no matter how it arrives — be it email, web, social media, SMS message or phone call — and no matter who it appears to be sent by.”
He explained that most social engineering attacks have two things in common. First, they arrive unexpectedly. The user wasn’t expecting it. Second, it’s asking the user to do something the sender — whomever they are pretending to be — has never asked the user to do before.
“It could be a legitimate request,” he continued, “but all users should be taught that any message with those two traits is at a far higher risk of being a social engineering attack, and should be verified using a trusted method, such as directly calling the person on a known good phone number.”
“If more organizations taught the two things to remember,” he said, “the online world would be a far safer place to compute.”
John P. Mello Jr. has been an ECT News Network reporter since 2003. His areas of focus include cybersecurity, IT issues, privacy, e-commerce, social media, artificial intelligence, big data and consumer electronics. He has written and edited for numerous publications, including the Boston Business Journal, the Boston Phoenix, Megapixel.Net and Government Security News. Email John.
Please sign in to post or reply to a comment. New users create a free account.
Yes
No
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/06/cyberwarfare-3-300×156.jpg
https://www.technewsworld.com/story/attacks-on-cloud-service-providers-down-25-during-first-4-months-of-2022-176678.html
Attacks on Cloud Service Providers Down 25% During First 4 Months of 2022
Canonical Lets Loose Ubuntu 22.04 LTS ‘Jammy Jellyfish’
Low-Code Platforms Help Ease the Shadow IT Adversity Pain
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/05/livestream-sports-300×156.jpg
https://www.technewsworld.com/story/study-finds-sports-is-king-among-livestreamers-176771.html
Study Finds Sports Is King Among Livestreamers
New Cisco Conferencing Devices Designed To Heal Meeting Fatigue
Amazon Puts High-Tech Spin on Play Dates With Kiddie Video-Calling Device
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/inflation-300×156.jpg
https://www.technewsworld.com/story/electronics-will-cost-more-in-2023-177026.html
Electronics Will Cost More in 2023
Apple Shows Off Vast Upgrades to Software, Hardware, User Experiences at WWDC22
Microsoft’s Innovative 4-Processor PC
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/customer-experience-300×156.jpg
https://www.technewsworld.com/story/how-not-to-do-cx-lenovo-style-177024.html
How Not To Do CX, Lenovo Style
Coding Vulnerabilities, Linux Growth, FOSS Friction Cap Summer Highlights
Security Demands Shifting Business Backups Away From On-Prem Boxes
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/Web3-security-300×156.jpg
https://www.technewsworld.com/story/forrester-report-cautions-about-web3-security-177005.html
Forrester Report Cautions About Web3 Security
IT Security Pros Push for Consolidated Standards, Vendor Products
5 Cyber Safety Tips To Survive the Internet, Hackers and Scammers
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/sysadmin-data-300×156.jpg
https://www.technewsworld.com/story/data-observabilitys-big-challenge-build-trust-at-scale-176667.html
Data Observability’s Big Challenge: Build Trust at Scale
The Business Case for Clean Data and Governance Planning
6 Critical Steps for Scaling Secure Universal Data Authorization
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/devops-300×156.jpg
https://www.technewsworld.com/story/leapwork-ceo-no-code-platforms-democratize-testing-automation-176913.html
Leapwork CEO: No-Code Platforms Democratize Testing Automation
Cognitive Skills for Engineering Success
Apple and Microsoft Developers Conferences Exhibit Companies’ Strengths, Weaknesses
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/solar-panel-home-300×156.jpg
https://www.technewsworld.com/story/the-coming-wave-of-next-generation-home-solar-companies-177031.html
The Coming Wave of Next-Generation Home Solar Companies
Accent Altering Voice Tech Aims To Replace Frustration With Communication
Qualcomm and the Mobile Video Game Revolution
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/accountant-300×156.jpg
https://www.technewsworld.com/story/b2b-funding-firms-banking-on-embedded-finance-176805.html
B2B Funding Firms Banking on Embedded Finance
Unresolved Conflicts Slow eSIM Upgrade Path to Better IoT Security
Cryptocurrency Custody Concerns: Who Holds the Digital Storage Keys?
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/gaming-rig-300×156.jpg
https://www.technewsworld.com/story/cloud-gaming-poised-for-takeoff-177028.html
Cloud Gaming Poised for Takeoff
Stat Firm Reports Less Than 1% of Subscribers Playing Netflix Games
Nvidia Showcases the Metaverse Future at GTC
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/cyberwarfare-2-300×156.jpg
https://www.technewsworld.com/story/chinese-hackers-deploy-fake-news-site-to-infect-government-energy-targets-177036.html
Chinese Hackers Deploy Fake News Site To Infect Government, Energy Targets
Top Universities Exposing Students, Faculty and Staff to Email Crime
6 Signs Cybercriminals Infected Your Phone and How To Fix It
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/06/KYY-Portable-Monitor-300×156.jpg
https://www.technewsworld.com/story/kyy-15-6-portable-monitor-packs-value-with-a-healthy-feature-set-176836.html
KYY 15.6″ Portable Monitor Packs Value With a Healthy Feature Set
New Linux Laptop Line Advances HP, System76 Open-Source Collaboration
InnoView’s 15.6″ 4K Portable Panel Could Be the Ultimate Touchscreen Accessory
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/07/covid-news-smartphone-300×156.jpg
https://www.technewsworld.com/story/meta-moves-to-back-off-removing-covid-misinformation-from-platforms-176937.html
Meta Moves To Back Off Removing Covid Misinformation From Platforms
Hack Your Metabolism To Improve Health With the Lumen Smart Device
Amazon Rolls Out Alexa for Senior Living and Healthcare Providers
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/07/home-security-300×156.jpg
https://www.technewsworld.com/story/home-security-market-thriving-despite-dread-of-false-alarms-176935.html
Home Security Market Thriving Despite Dread of False Alarms
Digital Devices of Corporate Brass Ripe for Hacker Attacks
Home Automation Faces 3 Perpetual Problems
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/04/code-tux-300×156.jpg
https://www.technewsworld.com/story/start-here-when-things-go-wrong-on-your-linux-system-176520.html
Start Here When Things Go Wrong on Your Linux System
Computers Use Processes, So Should You
NICE Platform Answers Call for Hyper-Personal CX Tools
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/06/canonical-ubuntu-300×156.jpg
https://www.technewsworld.com/story/ubuntu-core-22-release-addresses-challenges-of-iot-edge-computing-176583.html
Ubuntu Core 22 Release Addresses Challenges of IoT, Edge Computing
Foundries and Arduino Team To Patch IoT Devices
Remote Work Heightens Privacy and Security Anxiety Among Employees
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/press-conference-300×156.jpg
https://www.technewsworld.com/story/tech-whistleblowers-prefer-loud-exit-to-quiet-quitting-177039.html
Tech Whistleblowers Prefer Loud Exit To Quiet Quitting
Denmark Tops in Digital Quality of Life, US in Fifth Place
Unprotected Machine Identities Newest Enterprise IT Security Concern
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/05/microsoft-word-300×156.jpg
https://www.technewsworld.com/story/new-software-vulnerability-zeroes-in-on-microsoft-programs-176806.html
New Software Vulnerability Zeroes In on Microsoft Programs
Hackers Cast LinkedIn as Most-Popular Phishing Spot
Forrester Pegs B2B Fraud, Cyber Insurance Complacency as Top Threats in 2022
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/05/boy-screen-time-300×156.jpg
https://www.technewsworld.com/story/kids-screen-use-sees-fastest-rise-in-4-years-176735.html
Kids’ Screen Use Sees Fastest Rise in 4 Years
Sports Betting Platforms Gambling With Substandard CX
Appdome CEO on Mobile App Security: No Developer, No Code, No Problem
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/05/Titan-Linux-300×156.jpg
https://www.technewsworld.com/story/titan-linux-beta-brings-simplicity-finesse-to-kde-remake-176554.html
Titan Linux Beta Brings Simplicity, Finesse to KDE Remake
Linux Security Study Reveals When, How You Patch Matters
New Breeze Theme Gives KDE Neon Release Lots of Sparkle
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/04/personal-file-300×156.jpg
https://www.technewsworld.com/story/pii-of-many-fortune-1000-execs-exposed-at-data-broker-sites-176668.html
PII of Many Fortune 1000 Execs Exposed at Data Broker Sites
US-Led Seizure of RaidForums May Defy Lasting Effect on Security
Atlas VPN Debuts MultiHop+ for Added Layer of Internet Privacy and Security
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/03/apis-cor-3d-building-300×156.jpg
https://www.technewsworld.com/story/rebuilding-ukraine-3d-printing-and-the-metaverse-could-help-create-the-cities-of-tomorrow-87455.html
Rebuilding Ukraine: 3D Printing and the Metaverse Could Help Create the Cities of Tomorrow
InnoView 15.8″ Portable Display: More Screen Space for Small Devices
Desklab Portable Monitor: Ideal for Work, Play, Mobile Productivity
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/Space-BACN-300×156.jpg
https://www.technewsworld.com/story/darpa-moves-forward-with-project-to-revolutionize-satellite-communication-177003.html
DARPA Moves Forward With Project To Revolutionize Satellite Communication
Science, Art Inspire Women in Tech Entrepreneurship
Why Commercial Space Travel Is Unlikely To Scale Up
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/microsoft-bing-300×156.jpg
https://www.technewsworld.com/story/microsoft-bing-yandex-create-new-search-protocol-87311.html
Microsoft Bing, Yandex Create New Search Protocol
Botify SEO Platform Helps Brands Navigate Organic Search Rankings
Google Cloud Seeks To Cure Retailers’ Search Woes, Help Compete With Amazon
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/server-admins-300×156.jpg
https://www.technewsworld.com/story/cyber-asset-management-overwhelming-it-security-teams-87457.html
Cyber Asset Management Overwhelming IT Security Teams
30 Years of Linux History Told via Distros
Stale Open Source Code Rampant in Commercial Software: Report
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/03/digital-wallet-qr-code-300×156.jpg
https://www.technewsworld.com/story/whats-in-store-for-next-gen-digital-wallets-87451.html
What’s in Store for Next-Gen Digital Wallets
Apple Refreshes iPhone SE, iPad Air, Debuts Studio Desktop
Tesla Smartphone Could Be a Game Changer
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/social-media-apps-300×156.jpg
https://www.technewsworld.com/story/a-third-of-us-social-media-users-creating-fake-accounts-176987.html
A Third of US Social Media Users Creating Fake Accounts
Amazon Lawsuit Fingers Facebook Groups Recruiting Fake Reviewers
Big Tech Firms Move To Squash Deceptive Info on Ukraine Crisis
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/global-disaster-300×156.jpg
https://www.technewsworld.com/story/nvidia-launches-earth-2-and-goes-to-war-against-climate-change-87336.html
Nvidia Launches Earth 2 and Goes to War Against Climate Change
Kuo Predicts ‘iPhone 13’ Will Support Satellite Calls and Texting
30 Years Later, the Trajectory of Linux Is Star Bound
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/handwrytten-300×156.jpg
https://www.technewsworld.com/story/robotic-letter-writing-lends-a-hand-to-personalized-marketing-crm-176595.html
Robotic Letter Writing Lends a Hand to Personalized Marketing, CRM
Don’t Become a Fool in the IT Gold Rush
Marketers: Beware Florida’s Mini-TCPA
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/surface-duo-2-300×156.jpg
https://www.technewsworld.com/story/microsoft-finally-has-truly-competitive-alternatives-to-apple-products-87282.html
Microsoft Finally Has Truly Competitive Alternatives to Apple Products
New iPad Mini Stars at Apple Refresh Event
Chromebook Shipments Jump 75% YoY in Q2
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/07/tug-of-war-300×156.jpg
https://www.technewsworld.com/story/musk-twitter-qualcomm-apple-netflix-microsoft-deciphering-the-insanity-176915.html
Musk-Twitter, Qualcomm-Apple, Netflix-Microsoft: Deciphering the Insanity
The World Is Not Yet Ready for Electric Cars
The Importance of the Metaverse Standards Forum
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/04/eu-gavel-300×156.jpg
https://www.technewsworld.com/story/new-eu-law-will-force-google-meta-others-to-expose-algorithms-176689.html
New EU Law Will Force Google, Meta, Others To Expose Algorithms
Pandemic, Compliance Driving Increased Privacy Spending
Report Argues Antitrust Bill Would Hurt Consumers, Stymie Innovation
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/07/Lucid-Air-300×156.jpg
https://www.technewsworld.com/story/lucid-nvidia-and-the-rapidly-changing-future-of-electric-cars-176927.html
Lucid, Nvidia and the Rapidly Changing Future of Electric Cars
Rapid EV Adoption by Low-Income Drivers Needed To Curb Climate Change: Report
BlackBerry and Preparing for the Software-Defined Automobile
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/08/metaverse-future-300×156.jpg
https://www.technewsworld.com/story/nvidia-and-disney-can-breathe-life-into-the-metaverse-176993.html
Nvidia and Disney Can Breathe Life Into the Metaverse
The Metaverse Future: Are You Ready To Become a God?
New Recipe for Marketing Success: Blend Digital and CX, Mix Well With AI
https://www.technewsworld.com/wp-content/uploads/sites/3/2022/02/vr-metaverse-300×156.jpg
https://www.technewsworld.com/story/apple-mr-specs-will-shun-metaverse-report-87385.html
Apple MR Specs Will Shun Metaverse: Report
Apple Wearables Holiday Sales Knock It Out of the Park
5 Terrific Tech Gift Ideas for Your Holiday Shopping List
https://www.technewsworld.com/wp-content/uploads/sites/3/2021/07/xl-2016-hacker-2-300×184.jpg
https://www.technewsworld.com/story/cybercriminals-employing-specialists-to-maximize-ill-gotten-gains-87200.html
Cybercriminals Employing Specialists To Maximize Ill-Gotten Gains
Encouraging Research Finds Brain Adjusts to ‘Third Thumb’
E-Commerce Tending to Health and Wellness Needs
Copyright 1998-2022 ECT News Network, Inc. All Rights Reserved.
Enter your Username and Password to sign in.