LastPass provides details on August 2022 hack – Ghacks
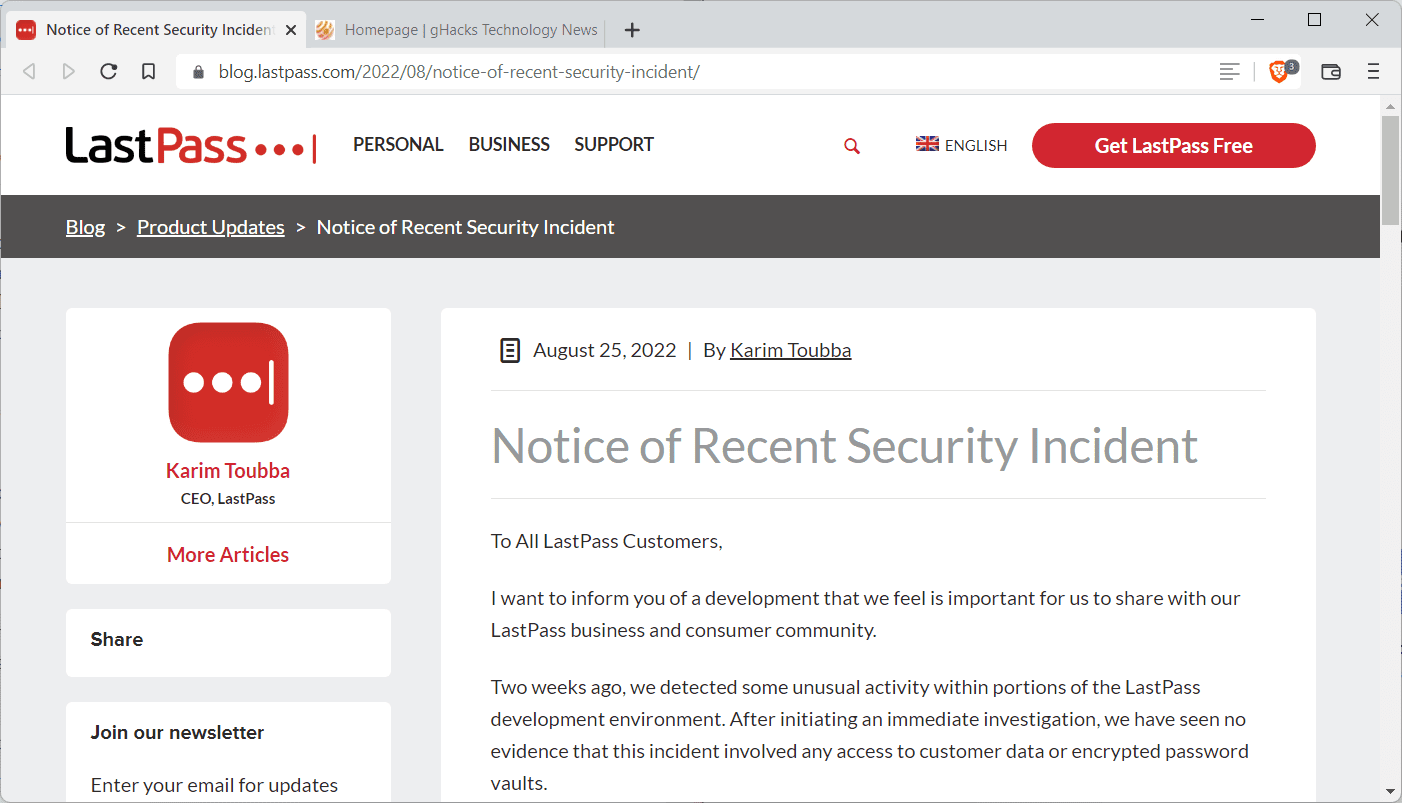
LastPass informed customers about a security breach on the company’s official blog in August 2022. This week, the company published additional information about the hack after its investigation.
The threat actor obtained “portions of source code and some proprietary LastPass technical information”, but could not access production environments or customer data.
LastPass asked the cybersecurity and forensics company Mandiant to assist them in the investigation of the incident. The September 2022 update reveals additional details about the security incident.
The threat actor gained access to the development environment for a 4-day period in August, according to LastPass. When LastPass security detected the incident, it was contained immediately.
No evidence was found that the threat actor had access beyond the 4-day period. Customer data and encrypted vaults were not accessed by the threat actor.
The attacker gained access through a compromised developer account. The account was protected with multi-factor authentication. Developer accounts are limited to the development environment, which prevented the threat actor from accessing customer data, encrypted vaults or production environments. Development environments have no access to customer data, according to LastPass.
Forensics experts analyzed the source code and production builds to determine whether any manipulation has taken place in the four day period. According to LastPass, it found “no evidence of attempts of code-poisoning or malicious code injection”.
As a security precaution, developers have no direct option to push source code from development to production. A separate build release team is responsible for that, which reviews, tests and validates sources and changes.
LastPass announced that it has improved security as a consequence.
As part of our risk management program, we have also partnered with a leading cyber security firm to further enhance our existing source code safety practices which includes secure software development life cycle processes, threat modeling, vulnerability management and bug bounty programs.
Further, we have deployed enhanced security controls including additional endpoint security controls and monitoring. We have also deployed additional threat intelligence capabilities as well as enhanced detection and prevention technologies in both our Development and Production environments.
Closing Words
While a threat actor gained access to LastPass’s development environment, they did not alter source code or gain access to customer data. Source code and technical information was accessed and obtained though.
Now You: which password management service do you use, if any? (via Born)
It begs the question: how was 2FA compromised on the developer account to enable access in the first place? It doesn’t seem from a read of this, that the account owner was tricked (or maybe they were?). Unlike at Twilo…
And this is why I choose offline password management. Not the first time either.
Another LastPass security breach?! Nothing on “the cloud” is safe. Security or convenience, you can pick only 1.
No site is 100% immune of being hacked so I won’t consider LastPass’ misfortune as an argument to avoid it.
If I opted for another Password Manager than LastPass it’s before all for easiness, usability and its Firefox extension’s size.
I use Bitwarden, intuitive, easy, excellent reputation, less than 9MB compared to Lastpass’ 39MB. I know techies will state that size doesn’t count when only the features should be considered. I’ve tried Lastpass several years ago and I recall a heavy structure not only in terms of size (though much liter then) but in usability : the thing was so complex, complicated in my view, compared to Bitwarden. Lastpass does maybe include features not found in Bitwarden (no idea) but in my experience Bitwarden, even in its free offer, provides all that I need.
Why not Firefox’s native Password Manager? Was my choice at one time but encountered several bothers (encryption strength, popup appearing and problematic to correctly setup) which made me consider opting for a dedicated extension, though I’m not really excited by any cloud service handling confidential data. Whatever my confidence in Bitwarden’s qualification there is confidential data I never handle to a cloud service, be it encrypted or not.
Please click on the following link to open the newsletter signup page: Ghacks Newsletter Sign up
Ghacks is a technology news blog that was founded in 2005 by Martin Brinkmann. It has since then become one of the most popular tech news sites on the Internet with five authors and regular contributions from freelance writers.